Beyond the Blackout Narrative: How Internet Infrastructure Is Reshaped During The Middle East Conflict
- MODAT Team

- Apr 15
- 7 min read

Introduction
The idea of an internet "blackout" is incomplete. In moments of geopolitical tension, networks rarely disappear entirely - instead, they are reshaped. What appears as disruption at the surface often reflects deeper structural changes in how infrastructure is exposed, controlled, and organised.
Most reporting focuses on absence: connectivity dropping, traffic disappearing, users being cut off. That framing is not wrong, but it is incomplete. It assumes that when connectivity is constrained, there is little left to observe. What the data across multiple countries in the region suggests is something different. Even under restriction, control, or operational pressure, the internet does not disappear entirely.
By extending the analysis beyond a single country to include Iran, Israel, Qatar, Saudi Arabia, the United Arab Emirates, Bahrain and Kuwait, a broader picture emerges. While each country exhibits distinct characteristics, the infrastructure graphs reveal consistent directional behaviour across the region and between Gulf countries.
What follows is based entirely on what is observable through Modat Magnify, no classified sources, no internal network access, no signals intelligence. Every conclusion drawn here reflects only what is visible from the outside.
Key Findings
Internet disruptions in conflict zones often reflect restructuring, not disappearance.
Countries exhibit distinct response patterns: mediation, deception, and stabilisation.
Understanding infrastructure behaviour requires analysing directional change over time, not static snapshots.
Method and Approach
This analysis is based on data collected through Modat Magnify. This allows for a longitudinal view of infrastructure behaviour, rather than a static snapshot.
To understand this behaviour, we analyse infrastructure across multiple countries using comparable time windows and identical query structures.
For each country, two periods are compared:
A baseline window representing steady state exposure in the first two months of 2026:
Example Query for Iran 1 Month Pre start of the conflict:
A subsequent window capturing shifts in infrastructure visibility and composition after the start of the conflict (28 of Feb 2026) and until the 27th of March 2026
Example Query for post start of the conflict:
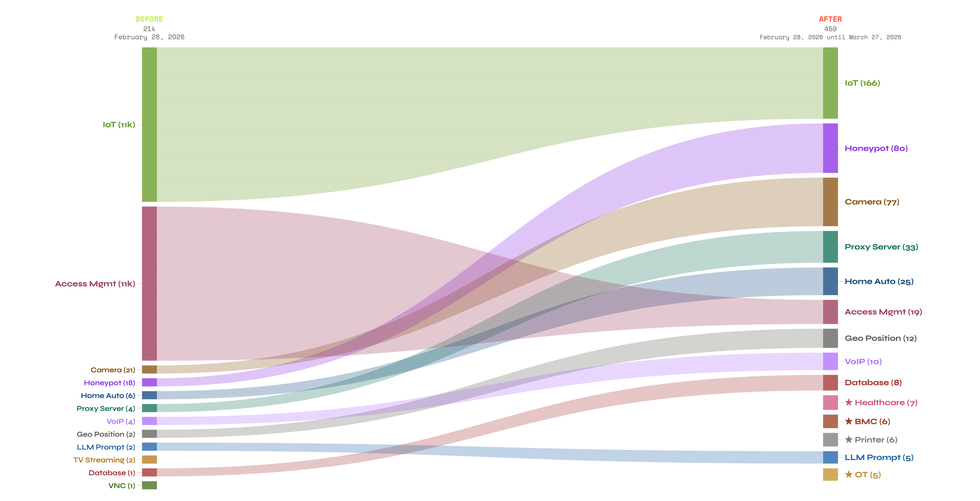
Rather than focusing on aggregate counts, the analysis tracks how infrastructure entities transition between categories over time, as visualised in Sankey graphs for each country.
This shifts the perspective from how much exists to how it changes.
Classification Framework
Infrastructure was categorised based on observable characteristics:
Standard Services: Public-facing, production-oriented services (e.g., Healthcare, Access Management, VNC, Proxies, Databases)
IoT Devices: Embedded or edge devices with identifiable signatures (e.g., cameras, routers, industrial systems)
Honeypots: Systems exhibiting characteristics consistent with deception or monitoring (e.g., known honeypot frameworks, anomalous service combinations, or behavioural signatures)
These classifications rely on Modat fingerprinting and should be interpreted as probabilistic rather than definitive.
With this framework in place, we can examine how these patterns manifest across different countries, each responding to pressure in distinct but comparable ways.
Analytical Constraints
It is important to note several limitations:
Observations are limited to externally visible infrastructure and do not reflect internal networks
Classification is based on Modat Magnify fingerprinting
Rapid changes in exposure may include scanning artifacts or temporary configurations
Visibility does not necessarily indicate operational importance or intent
With this analytical framework in place, we can examine how these structural shifts manifest across different countries. Each case reflects a distinct response to pressure, revealing how infrastructure is adapted rather than simply disrupted.
Infrastructure Transformation Under Pressure
While the same categories of infrastructure appear across all countries in the dataset, the way they evolve differs significantly.
The analysis reveals three distinct patterns: restriction-driven mediation, gradual restructuring, and active instrumentation.
Iran: From Exposure to Forced Mediation
In Iran, the graph reflects something more extreme than restructuring, it reflects effective disconnection. Following the escalation of the Middle East conflict, the country undergoes what is, in practice, a near-total internet shutdown. External visibility collapses, and what remains is not an open network, but a tightly controlled and highly selective system.
This is consistent with observed conditions on the ground, where internet traffic dropped to near-zero levels during the conflict, isolating the country from the global internet.
What the graph captures is what happens after that cutoff. The most interesting pattern is the surge in proxy layer infrastructure.
These proxies likely serve multiple roles:
Controlled gateways for the limited traffic that is still allowed.
Monitoring and filtering points for surveillance and censorship.
Potential routing layers for approved communication channels.
Fallback mechanisms for maintaining internal connectivity.
At the same time, the collapse of diverse application-layer categories suggests that most services are no longer directly reachable. It is not that they no longer exist, it is that they are no longer exposed.

Taken together, these changes point toward a coordinated transformation rather than isolated fluctuations. The reduction in direct exposure, combined with increased reliance on intermediary systems, is consistent with a shift toward controlled, mediated connectivity.
Israel: Rapid Expansion of Deceptive Surface Area, Maybe?
Israel presents a strikingly different profile, one defined not by withdrawal, but by deliberate and massive deception.
Between 28 Feb and 27 Mar 2026, total exposed infrastructure scaled from 2.6k to 71k entries, a ~27x increase. The dominant destination is Honeypot infrastructure, meaning the majority of what appears as exposed surface is intentional. Israel is not simply growing its attack surface; it is flooding the environment with decoys.
The observed 27-fold increase in systems classified as honeypots represents a significant shift in externally visible infrastructure.
This pattern is consistent with deliberate large-scale deployment of deceptive or monitoring systems. However, alternative explanations must also be considered, including classification bias, automated exposure of research environments, or rapid reconfiguration of existing infrastructure.
Rather than attributing intent directly, the key observation is structural: the external surface of the network expanded dramatically, with a disproportionate increase in assets that obscure, rather than clarify, the operational landscape.
The picture is of a potential deliberate, sophisticated strategy: flood the visible landscape with traps, harden what is real, and let adversaries exhaust themselves against ghosts.

Gulf Countries: Divergent Responses Across a Contested Region
Across the Gulf states, the most telling signals are not what disappeared but what surged:
Honeypot infrastructure surges prominently in the UAE, Saudi Arabia and Qatar, and appears as a new signal in several other countries where it was previously absent. The pattern mirrors what was observed in Israel, deliberately deployed decoy systems designed to attract, trap, and study adversarial probing activity. In a region experiencing elevated offensive cyber activity, flooding the visible landscape with fake targets serves a dual purpose: it wastes attacker resources and generates intelligence about who is probing, how, and with which tools.
The Camera trend extends beyond Saudi Arabia. Check Point Research recorded hundreds of exploitation attempts targeting Hikvision and Dahua cameras across Israel, UAE, Qatar, Bahrain, Kuwait, Lebanon, and Cyprus from late February onward. Whether these represent live operational assets or deliberate honeypots designed to fingerprint and track adversarial tooling remains an open question.
Proxy Server infrastructure grows across multiple countries simultaneously. This is relevant both for offensive operations moving through civilian-looking infrastructure and for defensive purposes of hiding the location of real systems behind intermediary nodes.
What unifies these surges is that none of them are passive. Cameras watch. Honeypots trap. Proxies route and obscure. Each category that grew across this region represents an active choice, infrastructure being deployed with intent, not merely left exposed by inertia.
The region is not simply reacting to conflict pressure; it is equipping itself to see, deceive, and manoeuvre within it.




Directional Behaviour, Not Random Change
The observed changes are not random fluctuations or noise inherent to internet-scale measurement. Instead, they exhibit directional consistency, multiple indicators shifting in alignment over time.
This coherence suggests underlying drivers rather than independent events, reinforcing the view that infrastructure is being actively reconfigured rather than passively disrupted.
This consistency across multiple indicators shifts the analysis from descriptive to explanatory. What initially appears as disruption begins to reveal itself as structured adaptation when observed over time.
Emerging Infrastructure Response Models
Across the observed countries, three distinct patterns of infrastructure behaviour emerge under stress:
Mediation Model (Iran) Infrastructure is reduced and funnelled through controlled intermediaries. Direct exposure decreases while reliance on proxies or gateways increases.
Deception Model (Israel) The observable attack surface expands, but clarity decreases. A significant portion of exposed infrastructure appears designed to mislead, monitor, or absorb interaction.
Stabilisation Model (Gulf States) Infrastructure remains largely available but undergoes gradual redistribution. Changes appear controlled and incremental rather than abrupt.
These models highlight that infrastructure control can be expressed in multiple ways: through restriction, expansion, or redistribution. While the external signals differ, each approach reflects an underlying effort to shape visibility, access, and interaction.
Conclusion
The concept of an “internet shutdown” is increasingly insufficient as an analytical framework.
These shifts suggest that future conflicts will not be defined by whether connectivity exists, but by how it is structured. The internet, in this context, becomes less a neutral medium and more an adaptive system, one that reflects the priorities, constraints, and strategies of those who control it.
As these patterns become more pronounced, the analytical challenge shifts as well. Measuring connectivity alone is no longer sufficient, understanding intent requires interpreting how infrastructure is shaped, not just whether it is present.
In this context, the internet is not simply disrupted during conflict, it is actively reshaped. What matters is not whether systems remain online, but how their structure evolves to reflect control, resilience, and strategy.
About Modat
Founded in 2024, Modat is a European research-driven cybersecurity company focused on strengthening cyber resilience for individuals, companies, and governments. Our flagship platform, Modat Magnify, fingerprints and catalogues every internet connected device, to turn large amounts of raw data into actionable security insights.
Modat was created by researching, listening to, and directly experiencing the needs and challenges of security professionals. Our products enable the security community by giving access to unparalleled speed, contextualised data, and predictive insights. We are actively joining the fight to get ahead of cyber-attacks by narrowing the growing gap between digital threats and resilience. Join us to outpace and outlast.
>> Learn more by visiting modat.io and to access the platform visit magnify.modat.io
Visit:

